In this article, I will overview the best blockchain provenance protocols to combat AI-generated deepfakes and increase digital trust in the era of AI. Such systems also verify the origin of content, track its source and record any manipulation done to media.
Solutions such as Numbers Protocol, C2PA and Truepic lay the foundation for transparent, secured and tamper-proof ecosystems that address issues of misinformation generation, processing and dissemination efficiently in today’s time.
Key Points & Best Blockchain Provenance Protocols To Fight AI-Generated Deepfakes
| Blockchain Provenance Protocol | 15-word Explanation |
|---|---|
| Numbers Protocol | Provides decentralized media provenance using blockchain and C2PA standards to verify authentic digital content. |
| Truepic | Verifies image authenticity through secure capture technology ensuring tamper-proof visual content provenance for media. |
| C2PA | Open standard embedding cryptographic metadata into media enabling verifiable content origin and modification tracking. |
| Story Protocol | Enables programmable intellectual property on blockchain ensuring ownership, licensing, and provenance of digital content. |
| Verisart | Certifies artworks and collectibles using blockchain-based certificates ensuring authenticity, ownership, and provenance verification records. |
| Artory | Secure digital registry recording fine art provenance data on blockchain for transparency and authenticity. |
| Starling Framework for Data Integrity | Uses blockchain and cryptographic tools to verify, secure, and preserve digital content authenticity records. |
| iExec Solutions | Decentralized computing platform ensuring trusted data processing with verifiable execution and secure provenance tracking. |
| Fact Protocol | Blockchain-based verification system enabling content authenticity, fact-checking, and combating misinformation and synthetic media. |
| OriginStamp | Timestamping service anchoring data hashes on blockchain ensuring immutable proof of existence and integrity. |
10 Best Blockchain Provenance Protocols to Fight AI-Generated Deepfakes
1. Numbers Protocol
Numbers Protocol provides a decentralized provenance infrastructure that records the lifecycle of digital media from capture to distribution. Blockchain and C2PA standards are wired together to verify the source of every image, video, or asset with a cryptographically secure tamper-evident history.
Its recent updates are focused on increasing its “Capture → Certify → Check” pipeline for AI-era content verification and machine-readable provenance. It also enables indexing of globally accessible storage and NFT-backed ownership records.
By attaching metadata and cryptographic hashes to the blockchain, it reduces deepfakes even with stripped metadata. Its ecosystem is being utilized more and more in journalism, elections and AI-generated content verification systems for the restoration of trust.
| Pros | Cons |
|---|---|
| Strong blockchain-based media provenance with C2PA integration | Requires ecosystem adoption for full effectiveness |
| Supports “capture → certify → check” lifecycle for content | Can be complex for non-technical users |
| Helps detect deepfakes by preserving origin metadata | Metadata still depends on proper capture at source |
| Used in journalism, elections, and AI content verification | Not fully effective if content is re-uploaded without credentials |
| Enables decentralized storage and immutable audit trails | Performance depends on network scalability |
2. Truepic
Truepic now provides an authenticity infrastructure that authenticates visual media at the point of capture with secure camera technology and cryptographic signing.
Its solutions natively embed tamper-proof metadata and C2PA-based content credentials directly into images and video. Recently, Truepic has been concentrating on combating the misuse of generative AI — both for its company and for our world at large — by empowering enterprise and media “verified capture” workflows.
It has partnered with AI safety organizations and led policy frameworks in synthetic media disclosure. Truepic is also engaged with C2PA standards as well and has tested cryptographically signed deepfake videos specifically for responsible AI use. This has made it a heavy-hitter when it comes to suppressing manipulated media from being treated as authentic evidence online.
| Pros | Cons |
|---|---|
| Verified capture technology ensures real-time authenticity | Requires dedicated capture environment or app |
| Strong enterprise adoption for media verification | Not suitable for already-created or edited content |
| Uses cryptographic signatures and C2PA credentials | Hardware/software limitations for general users |
| Effective against staged deepfakes at source | Less effective for redistributed media |
| Trusted by organizations for legal-grade evidence | Limited consumer-level accessibility |
3. C2PA
The Coalition for Content Provenance and Authenticity (C2PA) is an open technical standard that allows digital content to have its own verifiable record of who created it, when it was changed, who made the changes, and why.
It does this by embedding cryptographically signed metadata into media files, establishing a tamper-evident chain of custody. By 2026, C2PA is already everywhere through the major tech companies and media platforms — the backbone of content authenticity systems.

It is widely used for countering the AI-generated deepfakes as it provides me users to check whether the content is real or modified. And while it is not a product, its adoption across Adobe, Microsoft and others makes it a global standard for digital trust.
| Pros | Cons |
|---|---|
| Global open standard for content authenticity | Not a standalone tool—needs implementation by platforms |
| Embeds tamper-evident metadata into media files | Metadata can be stripped during uploads |
| Supported by major companies (Adobe, Microsoft, etc.) | Adoption still inconsistent across internet platforms |
| Helps verify origin and editing history of content | Does not prevent fake content creation itself |
| Highly scalable standard for AI-era media trust | Requires ecosystem-wide enforcement to be effective |
4. Story Protocol
Unchain uses blockchain-based provenance tracking to create programmable intellectual property for digital assets, particularly AI-generated content. It enables creators to register ownership, licensing rules and derivative rights, directly on-chain. In the age of AI, it is being used more commonly to govern attribution for generative content like images, music and text.
Its most recent direction involves integrating provenance-aware licensing systems that allow for AI outputs to be traced back to their sources and creators in training.
These measures minimize the misuse of deepfakes, while ensuring transparent revenue sharing. The future of AI-generated media with built-in ownership and traceable creative lineage is what Story Protocol is creating.
| Pros | Cons |
|---|---|
| Enables programmable intellectual property rights | Still emerging and not fully mature |
| Tracks ownership and licensing of AI-generated content | Complex legal integration challenges |
| Useful for managing AI-generated derivatives | Adoption depends on creator ecosystem growth |
| Supports attribution for generative content | Limited real-world enforcement today |
| Helps build transparent AI content economy | Regulatory clarity still evolving |
5. Verisart
Verisart is your blockchain-based certification of artworks, collectibles and digial assets, creating immutable proof-of-authenticity records. It enables artists and institutions to issue verifiable certificates that authenticate origin, ownership and history.
In recent times Verisart also entered the realm of digital art and NFT provenance to help curb AI-generated forgeries and impersonation in art. This will prevent any attempt of falsely attributing or manipulating an artwork by anchoring the certificates on blockchain.
Museums, galleries and creators deploy it to preserve trust in both the physical and digital art markets. In the deepfake era, it is key to demonstrating whether works of art are real or fake.
| Pros | Cons |
|---|---|
| Blockchain certificates for artworks and collectibles | Focused mainly on art and collectibles |
| Strong authentication for physical and digital art | Not designed specifically for real-time media verification |
| Prevents forgery and fake attribution | Limited deepfake detection capabilities |
| Used by galleries and museums | Requires onboarding by artists and institutions |
| Easy ownership verification | Less useful for fast-moving social media content |
6. Artory
Artory is a blockchain-based registry that provides secure data on provenance in the fine art market. It retains a tamperproof ledger of the ownership history, transactions, and authentication details of artworks.
Its recent efforts focus on embedding institutional-grade data for museums, auction houses and collectors to avoid frauds or forgeries. Amidst the rise of AI-generated art, Artory aids in differentiating between genuine artworks and synthetic reproductions by preserving authenticated historical records.
It partners with significant art institutions to increase transparency and trust in high-value digital and physical assets. Its system enhances market confidence by guaranteeing that provenance data cannot be modified or deleted.
| Pros | Cons |
|---|---|
| Secure fine-art provenance registry | Narrow focus on art market |
| Trusted by auction houses and institutions | Not optimized for AI-generated media verification |
| Strong fraud prevention for high-value assets | Limited scalability for mass digital content |
| Immutable ownership records | Slow adoption outside art industry |
| High institutional credibility | Not designed for real-time deepfake detection |
7. Starling Framework for Data Integrity
The Starling Framework — a blockchain-based data integrity system designed to maintain the authenticity of digital media artifacts for journalism and historical archiving. It issuescryptographic “birth certificates” for images and video, so that every adjustment is recorded.

Originally created with organizations including the USC Shoah Foundation, it has been used in investigative journalism and election documentation. And recent applications target the new forms of AI-enabled misinformation by securing media at the point of capture.
Starling is designed to preserve trustworthy evidence in the long run, so that potential 4th zeroing shady deepfakes and manipulated information can be easily identified against verified originals — both for courts of law and for newsrooms.
| Pros | Cons |
|---|---|
| Designed for preserving journalistic and historical evidence | Less consumer-friendly |
| Strong cryptographic verification of media integrity | Requires technical integration for deployment |
| Used in war crime and investigative documentation | Not widely adopted in social media platforms |
| Ensures tamper-proof media archives | Limited real-time verification features |
| Works well with blockchain + metadata systems | Focused more on archival than live content validation |
8. iExec Solutions
iExec GIF iExec offers decentralized cloud computing infrastructure for secure and verifiable execution of data and AI workloads. For deepfake prevention it offers a means of confidential computing whereby AI models can be run to process data without ever seeing or changing the data.
For instance, trusted execution environments (TEEs) developed recently can be used to verify the outputs generated by AI and ensure they have not been tampered with. In addition, decentralized oracles that can verify data integrity prior to consumption in applications are supported.
Through the combination of blockchain and secure computation, iExec guarantees that when AI systems produce or analyze media, they cannot silently manipulate provenance (the history of ownership), so it can be used to build both trustworthy AI pipelines and content verification systems.
| Pros | Cons |
|---|---|
| Enables secure decentralized computing for AI workflows | Not directly a provenance tool |
| Uses trusted execution environments (TEE) | Complex infrastructure requirements |
| Helps verify AI processing integrity | Requires developer-level integration |
| Supports confidential data handling | Limited end-user visibility |
| Useful for AI pipeline security | Indirect role in deepfake prevention |
9. Fact Protocol
Fact Protocol is a blockchain-centric verification system that aims to verify information, fight misinformation, and confirm claims about digital content. It enables decentralized fact-checking based on proof of existence and community-driven validation; data can be verified via cryptographic proofs.
Recently it has been optimized for the use of AI-content verification applications, including synthetic media and deepfake identification. Storing validation records on-chain provides a transparent audit trail for claims and media sources.
This allows platforms and users to determine whether content is accurate or doctored at a glance, helping preserve integrity in the information ecosystem during the generative AI age.
| Pros | Cons |
|---|---|
| Blockchain-based fact verification system | Still emerging with limited global adoption |
| Helps combat misinformation and fake media | Depends on community participation |
| Creates transparent audit trail for claims | Not focused on media capture integrity |
| Supports decentralized validation | Verification speed can vary |
| Useful for AI-era misinformation control | Needs stronger enterprise integration |
10. OriginStamp
OriginStampOriginStamp is a blockchain timestamping service that provides immutable proof of existence for digital files and data. It operates by hashing content and anchoring that to multiple blockchains
Making sure records cannot be altered or backdated. In some recent use cases, OriginStamp has even branched out into AI-era data integrity by helping prove that content — images, documents or videos — existed in a certain form at a specific time.
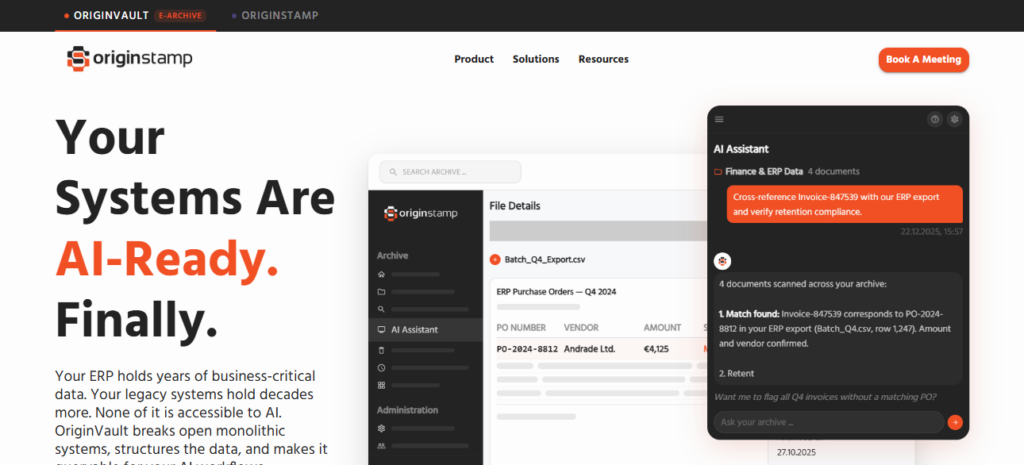
This means it can be used to prove original creation timestamps, making it useful for deepfake detection. This makes it common in legal, academic, and enterprise settings for audit logs and proofing.
| Pros | Cons |
|---|---|
| Immutable blockchain timestamping of data | Only proves existence, not authenticity |
| Strong proof-of-time for files and media | Cannot detect manipulation or deepfakes alone |
| Useful for legal and academic verification | Limited multimedia provenance features |
| Anchors data hashes across blockchains | Does not track editing history |
| Simple and widely usable | Needs complementary tools for full verification |
Cocnsluion
Conclusion Blockchain provenance protocols are essential for combating AI generated deepfakes by ensuring digital content authenticity, traceability and transparency. Technologies such as Numbers Protocol, C2PA and Truepic help to secure media authenticity throughout the lifecycle of the content from creation, distribution, verification until consumption.
No system is completely foolproof in preventing deepfakes, but these tools help substantially mitigate the risk of misinformation. The key to which with great adoption is necessary to build a trusted and tamper-proof digital information ecosystem in the world of AI.
FAQ
What are blockchain provenance protocols?
Blockchain provenance protocols are systems that record digital content origin, ownership, and edits using cryptographic and decentralized ledger technology.
How does Numbers Protocol work?
Numbers Protocol records media lifecycle from capture to distribution using blockchain and ensures tamper-proof provenance metadata.
What makes Truepic useful against deepfakes?
Truepic verifies images at the point of capture using secure camera technology and cryptographic signatures for authenticity.
Can C2PA completely stop fake content?
No, but it helps verify trusted content when metadata is preserved and supported across platforms and devices.