About Hanbiro
Hanbiro as a company specializes in providing server management services and enterprise software. They continuously strive to make sure you never regret choosing Hanbiro. Set up an exclusive communication system accessible by PC and mobile Integrate and manage all company documents in a central server. They offer optional services that customers can develop critical solution that they need most directly through the service experience of the long time. Your system administration team documents the impact analysis of various software upgrades and if any of them are perceived to have a high-risk, they are first beta-tested in your labs before live deployment.
While operating a server, maybe once or two times you used to be worry about a selecting suitable solution. Optional services are sold with verified excellent product or provided free for customers. High-quality services are provided by global software developers who have experience and technical skills of grown Hanbiro.
Some Quick Facts Hanbiro Web Hosting
| Hanbiro | Basic Details |
|---|---|
| Hosting Name | Hanbiro |
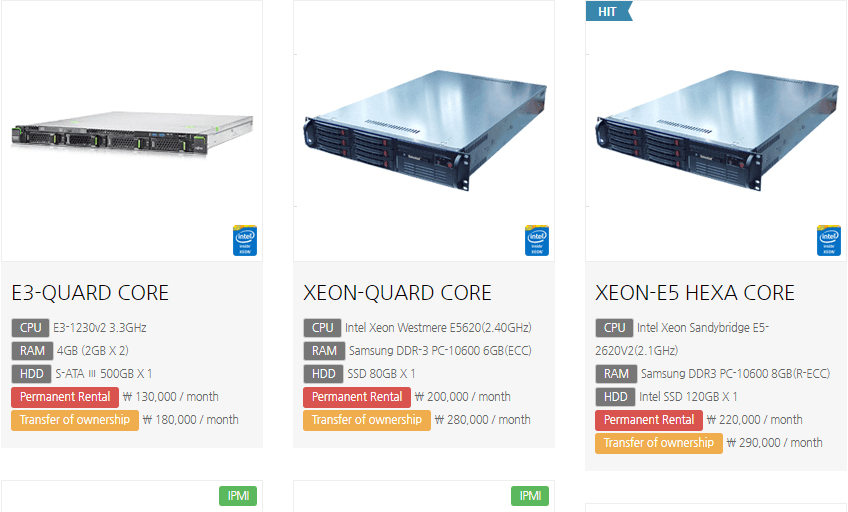
| Price | ₩ 180,000 / month |
| Support | 24/7 |
| English | English |
| Email Support | sori@hanbiro.com |
| Call Support | 070-4804-9691 |
| Official Website | Click Here To Visit |
Price
Technical support
Hanbiro is proud to provide customers with the latest specifications of the server and powerful optional services based on over 10 years of service management know-how. Please experience a fantastic mix directly with paid or free technical support. These and many such questions are regularly verified in an out-of-band process that involves investigation, surveys, ethical hacking attempts, interviews etc. Your audit mechanisms alert to a kink in your security processes before it is discovered by external users.
In a vast deployment of globally distributed servers, audit processes are required to ensure process replication and discipline. Are all servers being patched regularly? Are the backup scripts running all the time? Are offsite backups being rotated as desired? Are appropriate reference checks being performed on all personnel? Is the security equipment sending out timely alerts?
Personnel Security
Theweakest link in the security chain is always the people you trust. Personnel, Development staff, Vendors, essentially anyone that has privileged access to your system. Your Holistic Security Approach attempts to minimize security risk brought on by the “Human Factor”. Information is divulged only on a “need-to-know” basis. Hanbiro Authorization expires upon the expiry of the requirement. Personnel are coached specifically in security measures and the criticality of observing them.
Every employee that has administrator privileges to any of your servers goes through a comprehensive background check. Companies that skip out on this are putting to risk all sensitive and important data belonging to their customers, as no matter how much money is invested into high-end security solutions, one wrong hire – having the right amount of access – can cause greater damage than any external attack.
Application Security
All of the application software that is used in the platform is built. They do not outsource development. Any 3rd party Products or Components go through comprehensive training and testing procedures where all elements of such products are broken down and knowledge about their architecture and implementation is transferred to your team. This allows to completely control all variables involved in any particular Product. All applications are engineered using your proprietary Product Engineering Process which follows a proactive approach towards security.
Each application is broken down into various components such as User Interface, Core API, Backend Database etc. Each layer of abstraction has its own security checks, despite the security checks performed by a higher abstraction layer. All sensitive data is stored in an encrypted format. Your engineering and development practices ensure the highest level of security with regards to all application software.
Software Security
All servers are registered for automatic updates to ensure that they always have the latest security patch installed and that any new vulnerabilities are rectified as soon as possible. Hanbiro largest number of intrusions result from exploitation of known vulnerabilities, configuration errors, or virus attacks where countermeasures ARE already available. According to CERT, systems and networks are impacted by these events as they have “not consistently” deployed the patches that were released.